The PyeongChang 2018 Winter Olympics were close to starting off on a bad note had hackers behind a cyber-attack that occurred during the March 9 opening ceremony harbored greater ill-intentions. (Image: Yonhap)
SEOUL, March 21 (Korea Bizwire) — The PyeongChang 2018 Winter Olympics were close to starting off on a bad note had hackers behind a cyber-attack that occurred during the March 9 opening ceremony harbored greater ill-intentions.
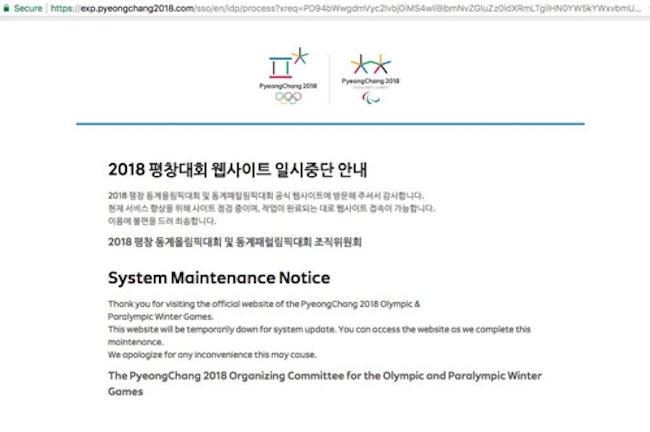
Named “Olympic Destroyer”, the malicious code caused IPTVs in the Olympic Main Press Center to switch off and made inaccessible the PyeongChang Olympics organizing committee website. The hackers stole user data stored in the infiltrated database.
According to threat researcher Earl Carter of Cisco’s cybersecurity arm Talos, the forces behind the Olympic cyber security breach were out to send a message.

According to threat researcher Earl Carter of Cisco’s cybersecurity arm Talos, the forces behind the Olympic cyber security breach were out to send a message. (Image: Yonhap)
“It looks as though the attackers wanted to avoid a worst case scenario and rather were of the mindset of ‘giving [the Olympics] just a taste’,” said Carter at Asem Tower in Gangnam on March 20.
Carter explained, “An analysis revealed that the code was written to delete only the files of the file sharing system, and to leave the files held within the system alone. There was sufficient capability of causing greater mayhem, it’s just that [the hackers] chose not to do so.”
Ever since, fingers have pointed to Russia or North Korea as behind the attack, but Carter believes identifying the ones responsible is easier said than done, as cyber terrorists can incorporate elements distinct to various countries into their code.
While all internet users are recommended to take extra precautions when conducting online activity, users of cryptocurrency and IoT devices are particularly encouraged to do so, as the two technologies are considered the chief targets of hackers.
Most hackers use phishing websites when aiming for cryptocurrency traders. Blockchain-related phishing websites are built and placed at the top of Google search result lists to lure in unwitting internet users.
One example of this method is www.blockchien.info, a phishing site that was determined by Cisco to have been visited by hundreds of thousands of visitors. Internet users are automatically redirected to a legitimate cryptocurrency web service, where the cryptocurrency wallets they create are secretly controlled by hackers.
The originating source of this scam was found to be in Ukraine, with almost $50 million having been siphoned off over three years.
With IoT devices expected to number 27.1 billion by 2021 and given that the majority of these products are manufactured without much concern for digital security, Carter said protective measures need to be taken seriously at the development stage.
Kevin Lee (kevinlee@koreabizwire.com)